Want to get immediate actionable insights on how to improve your Azure security? Try out our free Azure Snapshot tool to get security, monitoring, and cost optimization score with actionable insights!
Security is a primary concern when businesses first approach us about optimizing their Azure infrastructure. As their infrastructure grows, so does their awareness of potential security vulnerabilities, data leaks, and breaches of privacy regulations.
Azure operates a shared responsibility security model. The division of responsibility depends on the service, with IaaS putting the majority of the security burden on the user. With PaaS services, Microsoft takes over some aspects, including the operating system and network security. Whichever services a business uses, it’s vital to where the division of responsibility lies and the areas they should focus on to mitigate potential security risks.
Azure Security Center helps users to identify areas of concern. It is a unified security management system designed to help Azure users to strengthen their security posture and address their most pressing security challenges. Among Azure Security Center’s capabilities—in addition to monitoring and alerting—are proactive security recommendations based on an assessment of the user’s infrastructure.
Azure Security Center Quick Wins
Security is a journey, a long-term effort to extend penetration times and reduce the potential attack surface area. We recommend defense-in-depth with a layered approach that applies security strategies at all levels of the infrastructure and software stack, not just at network boundaries.
Security Center’s proactive recommendations are an excellent starting point for Azure security optimization. Our approach to Security Center recommendations breaks them into four categories, which we help our clients to tackle in turn. We start with low-cost, easy wins that bring security benefits without disrupting operations and the user experience, before moving on to more in-depth optimizations.
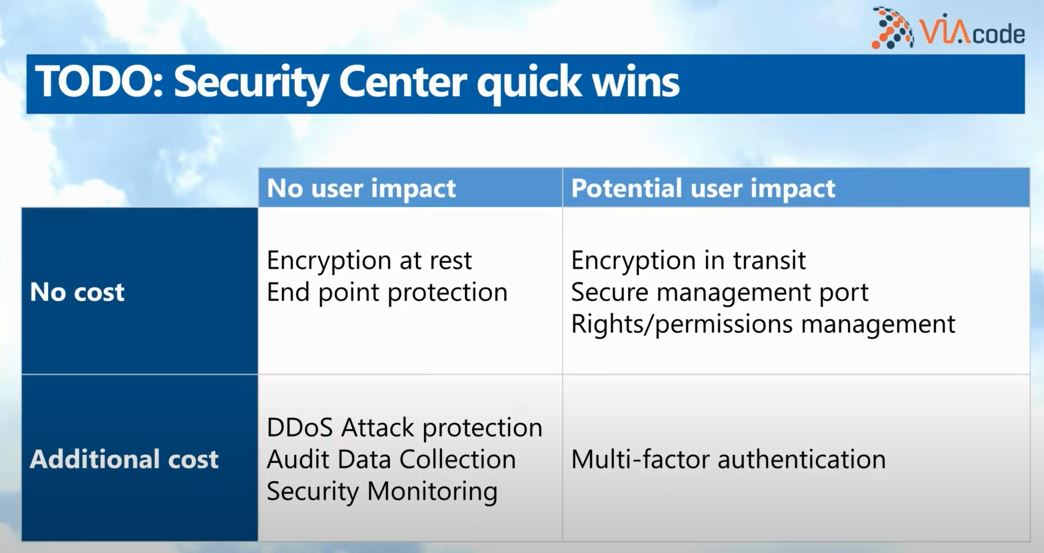
No Cost, No User Impact
This category includes high-impact, low-cost security optimizations. They are the fastest optimizations to implement, even though they significantly reduce security and data privacy risks.
- Encryption at rest — All data should be encrypted at rest. Encryption at rest keeps data safe in the event of a security breach. Encryption at rest is free on Microsoft Azure, with no impact on user experience.
- Endpoint protection — Azure Endpoint Protection enables anti-malware tools on Azure VMs that are connected to Azure Security Center. It’s free, low-impact, and helps businesses to identify security breaches quickly.
No Cost, Potential User Impact
Some mitigations are free but have the potential to impact the user. They may disrupt operations or require additional testing or training. For example, implementing encryption in transit may break applications without careful consideration of how services interact.
Quick wins in this category include:
- Encryption in transit — Data should be encrypted as it travels over the network, either to endpoints or between services. Network communication on Azure may already be encrypted by default, but under the shared security model, users are responsible for implementing TLS encryption for their apps and in some other areas.
- Rights and permissions management — Intelligent management of access to Azure resources ensures that only essential users have access to critical infrastructure.
We help clients to implement these recommendations and manage their potential impact.
Additional Cost, No User Impact
After implementing free, high-impact quick wins, we advise clients to deepen their security with Azure’s paid features, beginning with those with the least potential to disrupt operations. They include:
- DDoS Attack Protection — Azure DDoS Protection is a scalable, multi-layered DDoS mitigation service that can defend against distributed denial of service attacks at the network and application layer.
- Audit Data Collection — Data collection uses log analytics agents to collect data from virtual machines and containers to monitor for potential security vulnerabilities.
Additional Cost, Potential User Impact
Finally, we recommend that businesses shift focus to Security Center recommendations that have an additional cost and that may disrupt operations or require testing and training. They include Azure features such as multi-factor authentication, which can substantially reduce the likelihood of unauthorized bad actors gaining access to a business’s Azure infrastructure.
In Conclusion
The ultimate goal of the security journey is to implement security protections, best practices, and monitoring throughout the infrastructure and software stack. By implementing Azure Security Center recommendations, businesses improve their security posture over time, radically reducing their exposure to data theft, compromised infrastructure, and breaches of data privacy regulations.
To learn more about how VIAcode managed services can optimize security for your Azure infrastructure, contact an Azure security specialist today.