Azure Network Security Groups (NSGs) are flexible firewall rules users can apply to subnets and resources within an Azure Virtual Network. They allow users to specify which incoming and outgoing connections should be allowed or denied.
Microsoft has excellent documentation that describes how to configure and apply a Network Security Group, so we’re going to focus on the concepts that will help you to understand them, what they do, and the role they play in securing Azure infrastructure. Let’s start with Virtual Networks.
What is a Virtual Network in Azure?
A Virtual Network (VNet) is a virtual representation of the networks that we use in our homes and businesses. In a real-world network, a router mediates incoming and outgoing connections. Other devices such as servers or laptops are on a private network “behind the router,” and are not directly accessible to incoming connections from the internet or other private networks.
VNets are conceptually similar, and they are used to connect and isolate groups of resources. A resource such as a virtual machine has a private IP address drawn from a pre-determined address space so it can communicate with other resources in the same network. Private IP addresses cannot be accessed from outside the network, but resources can be assigned public IPs for incoming connections. You could also use load balancers, a bastion server, Azure Bastion, or some other “gateway” to mediate communication between the private network and the internet.
It’s worth noting that several Azure services can be deployed into or integrated with a Virtual Network, not only VMs. These include Azure Logic Apps, Web Apps, containers, Azure Firewall, and more.
Within a VNet, you can create multiple subnets. Subnets divide the Virtual Network into segments, and every VNet has at least one subnet. Resources such as virtual machines are deployed into subnets, each of which uses a portion of the virtual network’s address space for their private IPs.
Subnets are an important concept because Network Security Groups can be applied to subnets or a resource’s network interface, but not to entire virtual networks. However, if your needs are simple, you can put all of your resources into one subnet.
What is a Network Security Group?
Network Security Groups allow you to define a set of security rules and then them at the subnet or resource level. You can apply multiple Azure security groups to each subnet or resource network interface, and apply each security group to many subnets and resources.
Security rules include the following properties: priority; source and destination IP, IP block, or service tag; protocol; direction—inbound or outbound; port range; and action—allow or deny.
Let’s look at one of the default rules that all Azure security groups include:
| Priority | Source | Source Ports | Destination | Destination Ports | Protocol | Access |
| 65000 | VirtualNetwork | 0–65535 | VirtualNetwork | 0–65535 | Any | Allow |
This rule allows any connections from any port of any private IP on the VNET to any destination within it. Essentially, it opens the doors to connections from other resources. It’s easy to see why that is a useful default, but note the very high number in the priority field. Users can assign priorities from 100 to 4096. The higher the number, the lower the priority. High priority rules override conflicting lower priority rules, so any rule you create within a network group will override this example.
Security groups are fundamental to Azure security because they let you precisely control inbound and outbound traffic with far more flexibility than if you had to manage access to each resource individually.
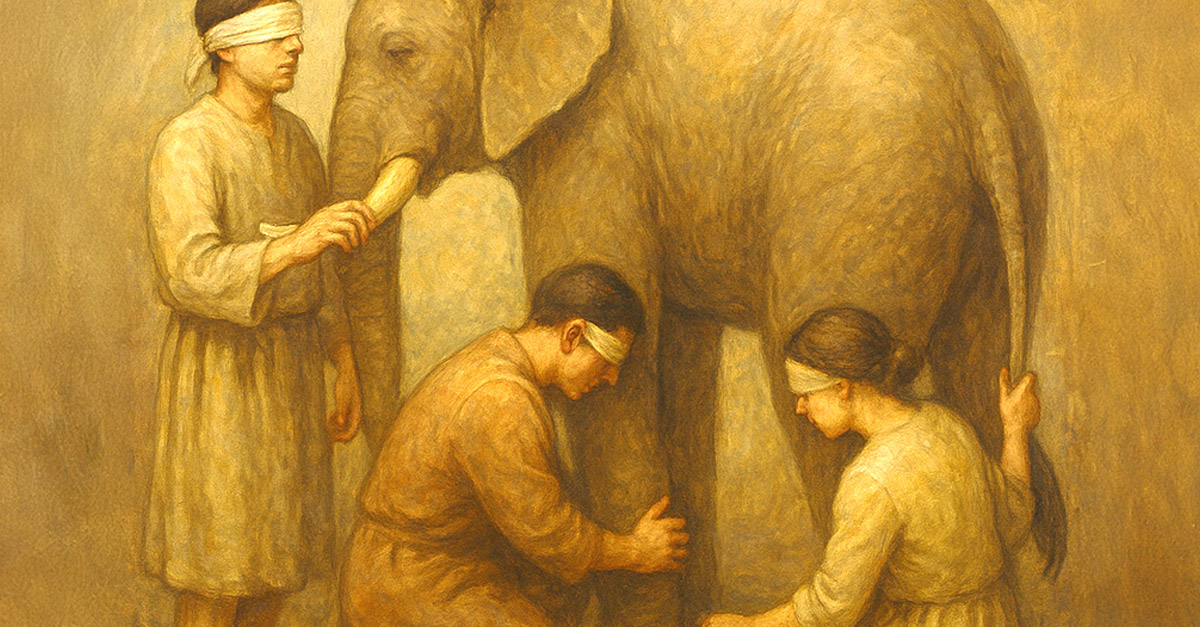
Earlier we compared Network Security Groups to a firewall, which might make you wonder about the difference between NSGs and Azure Firewall. Do they do the same job? Do you need NSGs if you use Azure Firewall? In fact, NSGs and Azure Firewall are complementary. With NSGs, you can apply network-level filters to control traffic within your virtual networks. Azure Firewall is a managed Firewall-as-a-Service that implements a powerful stateful firewall that provides network and application-level filtering. Together, they enable you to deploy a defense-in-depth approach with multi-level protection.
Azure Security Services
Network Security Groups are just one of the security, privacy, and compliance services that Azure provides. At VIAcode, we help businesses leverage Azure to build and manage secure and reliable infrastructure platforms.
To learn more, contact an Azure security specialist today or take our free Azure Snapshot health check for security and performance recommendations tailored to your infrastructure.